 Beware
of "Phishing"
Beware
of "Phishing"
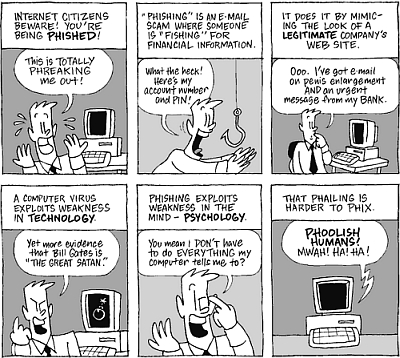
 t is becoming increasingly common to tune in to the news or load
your favorite news Web site and read about yet another Internet
e-mail scam. An e-mail scam is a fraudulent e-mail that appears to
be from a legitimate Internet address with a justifiable request —
usually to verify your personal information or account details.
t is becoming increasingly common to tune in to the news or load
your favorite news Web site and read about yet another Internet
e-mail scam. An e-mail scam is a fraudulent e-mail that appears to
be from a legitimate Internet address with a justifiable request —
usually to verify your personal information or account details.
One example would be if you received an e-mail that appears to be
from your bank requesting you click a hyperlink in the e-mail and
verify your online banking information. Usually there will be a
repercussion stated in the e-mail for not following the link, such
as "your account will be closed or suspended". The goal of the
sender is for you to disclose personal and (or) account related
information. This type of e-mail scam is also called phishing.
Phishing (fish´ing) (n.)
The act of sending an e-mail to a user
falsely claiming to be an established legitimate enterprise in
an attempt to scam the user into surrendering private
information that will be used for identity theft. The e-mail
directs the user to visit a Web site where they are asked to
update personal information, such as passwords and credit card,
social security, and bank account numbers, that the legitimate
organization already has. The Web site, however, is bogus and
set up only to steal the user’s information.
 How to Spot A Phishing Scam
How to Spot A Phishing Scam
At first glance, it may not be obvious to the recipients that what
is in their inbox is not a legitimate e-mail from a company with
whom they do business. The "From" field of the e-mail may have the
.com address of the company mentioned in the e-mail, and the
clickable link may also appear to be taking you to the company's Web
site, but will in fact take you to a spoof Web site. Looks can be
deceiving, but with phishing scams the e-mail is never from who is
appears to be!
 1. The "From Field" appears to be from the legitimate company
mentioned in the e-mail. It is important to note, however, that it
is very simple to change the "from" information in any e-mail
client. While we're not going to tell you how, rest assured it can
be done in a matter of seconds!
1. The "From Field" appears to be from the legitimate company
mentioned in the e-mail. It is important to note, however, that it
is very simple to change the "from" information in any e-mail
client. While we're not going to tell you how, rest assured it can
be done in a matter of seconds!
 2. The e-mail will usually contain logos or images that have been
taken from the Web site of the company mentioned in the scam e-mail.
2. The e-mail will usually contain logos or images that have been
taken from the Web site of the company mentioned in the scam e-mail.
 3. The e-mail will contain a clickable link with text suggesting you
use the inserted link to validate your information. In the image you
will see that once the hyperlink is highlighted, the bottom left of
the screen shows the real Web site address to which you will go.
Note that the hyperlink does NOT point to the legitimate Citibank
Web site URL.
3. The e-mail will contain a clickable link with text suggesting you
use the inserted link to validate your information. In the image you
will see that once the hyperlink is highlighted, the bottom left of
the screen shows the real Web site address to which you will go.
Note that the hyperlink does NOT point to the legitimate Citibank
Web site URL.
In this instance the text you click is "here", however this may also
state something like "Log-in to Citibank" or
"www.citibank.com/secure" to be even more misleading. This clickable
area is only text and can be changed to anything the sender wants it
to read.
Elements that did not appear in this particular scam:
* Logos that are not an exact match to the company's
logo... spelling errors, percentage signs followed by
numbers or @ signs within the hyperlink, random names or e-mail
addresses in the body of the text, or even e-mail headers which
have nothing to do with the company mentioned in the e-mail.
* Language and tone. The message you receive may urge you
to act quickly by suggesting that your account is threatened. It
may say that if you fail to update, verify or confirm your
personal or account information, access to your accounts will be
suspended. The wording may also be sloppy and contain
misspellings.
* Requests for personal information. Scam e-mails typically
ask for personal or account information such as:
- Account numbers
- Credit and check card numbers
- Social Security numbers
- Online banking user IDs and passwords
- Mother's maiden name
- Date of birth
- Other confidential information
* E-mailed instructions to download software. All your
online banking should be done through our secure Web site, and
we will not send you e-mail instructions to download any banking
software to your computer. Do not install software downloads
directly from e-mail messages, or from companies or Web sites
you do not recognize. When in doubt, contact the company
directly or call our customer service number at 800.788.7000.
* Non-secure Web pages. Clever thieves can build a fake
Web site that looks nearly identical to an authentic one. They
can even alter the URL (the Web address) that appears in your
browser window. Watch out for non-secure Web pages that ask for
sensitive information (secure sites will typically display a
lock in the status bar at the bottom of your browser window).
General Security Tips
 Never give out personal information online or over the phone unless
you have initiated the contact. Some Banks will never request that
you submit confidential information over non-secure channels such as
e-mail or phone calls initiated by them.
Never give out personal information online or over the phone unless
you have initiated the contact. Some Banks will never request that
you submit confidential information over non-secure channels such as
e-mail or phone calls initiated by them.
 Don't include information such as your driver's license or Social
Security Number on your pre-printed checks.
Don't include information such as your driver's license or Social
Security Number on your pre-printed checks.
 Memorize all Personal Identification Numbers (PINs), such as your
ATM card PIN and online passwords. Do not keep such numbers in your
wallet or purse.
Memorize all Personal Identification Numbers (PINs), such as your
ATM card PIN and online passwords. Do not keep such numbers in your
wallet or purse.
 Avoid using easily guessed or learned information such as your
online password, PIN or Telephone Access Code (TAC).
Avoid using easily guessed or learned information such as your
online password, PIN or Telephone Access Code (TAC).
 Get the ability to select a TAC to be used as identification when
accessing our automated phone system. We encourage you to select a
TAC rather than using your Social Security number
Get the ability to select a TAC to be used as identification when
accessing our automated phone system. We encourage you to select a
TAC rather than using your Social Security number
 Store new and cancelled checks in a secure place and shred
unnecessary financial documents. Consider signing up for a check
safekeeping service.
Store new and cancelled checks in a secure place and shred
unnecessary financial documents. Consider signing up for a check
safekeeping service.
 Avoid writing your account number on envelopes or other items that
may be thrown away later.
Avoid writing your account number on envelopes or other items that
may be thrown away later.
 Register your credit cards, ATM, check and debit cards with a
liability protection service.
Register your credit cards, ATM, check and debit cards with a
liability protection service.
 If you stop receiving bills, statements or other monthly mailings,
or if a bill is not received when expected, contact the issuing
company immediately.
If you stop receiving bills, statements or other monthly mailings,
or if a bill is not received when expected, contact the issuing
company immediately.
 Promptly collect incoming mail, and use a locking mailbox if
possible.
Promptly collect incoming mail, and use a locking mailbox if
possible.
 Send outgoing mail from a secured mailbox or a post office; try to
avoid leaving outgoing mail in your home mailbox.
Send outgoing mail from a secured mailbox or a post office; try to
avoid leaving outgoing mail in your home mailbox.
 Shred all unwanted pre-approved offers for credit cards, convenience
checks or loans.
Shred all unwanted pre-approved offers for credit cards, convenience
checks or loans.
Passwords and User IDs
Avoid these when creating passwords:
* Your birth date or a family member's birth date
* Names of family members or pets
* Social Security number
* Phone numbers
* Dates of important events, such as anniversaries
Tips for creating strong passwords:
* Use a combination of numbers, letters and punctuation.
* Longer passwords are better.
* Make sure it's something you can remember without writing it
down.
|
Protect
Your PC
 |
Install
and Use
Internet Security Programs
Viruses can infect a home computer in many ways: through floppy
disks, CDs, e-mail, Web sites and downloaded files. Anti-virus
programs help protect your computer against most viruses, worms,
Trojans and other unwanted invaders that can make your computer
"sick." Viruses, worms and the like often perform malicious acts,
such as deleting files, accessing personal data or using your
computer to attack other computers. If a file is found to be
infected with a virus, most anti-virus programs provide you with
options of how to respond, such as removing the harmful item or
deleting the file. Installing an anti-virus program and keeping it
up-to-date is the best defense for your home computer.
Firewalls: What Are They and How Do I Use Them?
Before you connect your computer to the Internet, you should install
a firewall. A firewall can be generally described as a security
guard for your home computer. The guard is a piece of software or
hardware that helps protect your PC against hackers and many
computer viruses and worms. With a firewall, you define which
connections between your computer and other computers on the
Internet are allowed and which are denied. There are firewall
programs, both free and available for purchase, that provide the
capabilities you need to help make your home computer more secure.
Decrease risk of being a phishing victim
Here are some more safety tips:
* Be suspicious of demanding messages. Messages threatening to
terminate or suspend your account without your quick response should
be treated as suspicious. A legitimate bank or business should not
request personal information from you over an unsecured Web site.
When in doubt, call the business' customer service number (available
on your account statement) to confirm the status of your account. Do
not use telephone numbers found on the suspected Web site.
* Be cautious of downloads. Installing unknown software on your
computer can put your personal information at risk and potentially
harm your computer's hard drive. Make sure the software comes from a
legitimate Web site, not an e-mail message. If you're not sure
whether you should download a program, contact a customer service
representative for more information.
* Always type in the URL of the Web page you need. Phishing scams
rely on embedded links that take you to fake Web sites. It's safer
to type your bank's Web address directly into your browser so you
know you're visiting the legitimate site.
* Protect your password. Don't write down sensitive personal
information such as your password or Social Security number. Change
your password frequently.
* Keep your computer up-to-date. Washington Mutual recommends that
you install anti-virus and firewall programs to help keep your
computer safe. Learn more.
Report an online scam
If you receive suspicious e-mail, do not open any attachments or click any
links found in the suspicious e-mail.
You may also want to forward it to the Federal Trade Commission at
spam@uce.gov, or contact them at
www.consumer.gov/idtheft
* or 877.IDTHEFT (877.438.4338).
If you believe you have provided personal or account information in
response to a fraudulent e-mail or Web site, please contact
Washington Mutual at 800.788.7000 and contact the other financial
institutions with which you have accounts.
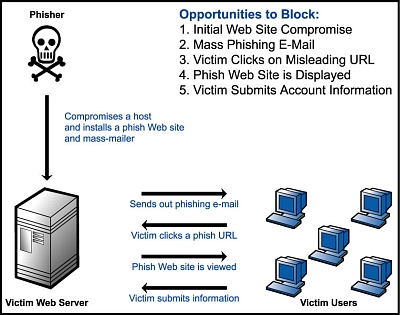
Learn more about phishing
To learn more about phishing, read the phishing brochure* provided
by The Office of the Comptroller of the Currency (OCC). The OCC
charters, regulates and supervises all national banks.
Purchasing and Installing Programs
Apply these practices when you select software for your home
computer.
* Learn as much as you can about the product and what it does before
you purchase it.
* Understand the refund/return policy before you make your purchase.
* Buy from a local store that you already know or a national chain
with an established reputation.
Keep Your System Up-to-Date
Most software vendors provide free patches to fix problems in their
products. You can usually download these patches from the vendor's
Web site. When you purchase a program, it's a good idea to find out
how the vendor provides customer support.
Backups: How Important?
It is a good practice to back up important files and folders on
your computer. To back up files, you can make copies onto media that
you can safely store elsewhere, such as CDs or USB Flash Drives.
1 GIG - Holds around 2,000 pages of text
Fits on key chain - less than $20.00


Share this with a friend...
HERE


P r o t e c t Y o u r P C

Peace and Prosperity,
Don Jíbaro "Whodatman" Barbanegra
www.jibaros.com
www.whodatman.net

~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
"The wicked run when no one is chasing them,
but the honest are as brave as lions." —Book of Proverbs 28:1
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~


“Live in such a way that no one blames the rest of us
nor finds fault with our work.” --(2 Corinthians 6:3)

Jibaros.Com®,
Jibaros.Net® -
This website all its contents and artwork is Copyright © by
Orlando Vázquez, owner-designer. All rights reserved by the respective sources.
Derechos Reservados de los Autores. Jibaros.com does not accept
any responsibility for the privacy policy of content or services
provided by third party sites. - U.S. Copyright Office, 101
Independence Ave. S.E. Washington, D.C. 20559-6000.
HX-006699

